Introducing Lexa 2.0
DNS & HTTP Service Discovery for LXD Containers
DNS & HTTP Service Discovery for LXD Containers
Easily create material lists for Minecraft Bedrock .mcstructure files
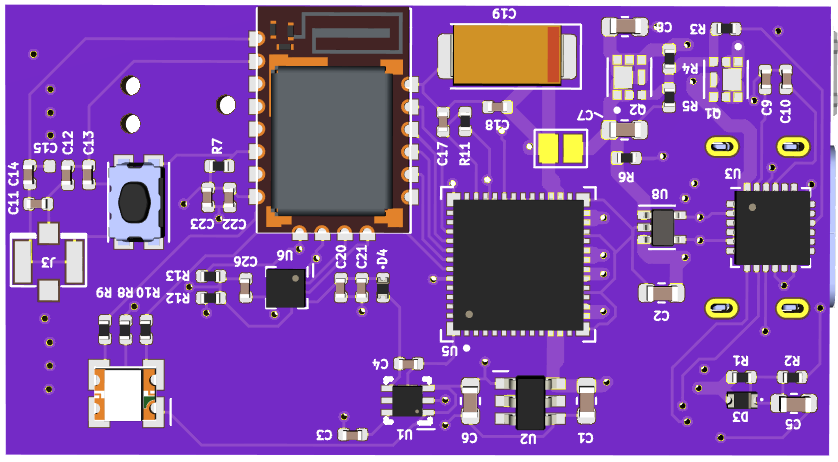
A USB-C PD powered, Bluetooh controlled motor driver and IO software and hardware.
Today I am making source-available one of my pandemic projects - pbrick – a USB-C PD powered, Bluetooh controlled motor driver and IO software and hardware.
A better bootloader for nRF52 chipsets
Today I am publicly announcing the availability of a new nRF52 bootloader for nRF52840 circuits, which source code and binaries available at: https://github.com/kaidyth/nrf52_bootloader.
DNS & HTTP Service Discovery for LXD Containers
Fully secure your home DNS traffic with CoreDNS
Your DNS server knows a lot about you - in fact it knows every single website your visit. Between ISP’s intercepting both valid and invalid domains, and potentially selling your browsing history to advertisers, it’s both prudent and remarkably simple to encrypt all of your DNS to prevent this and to more importantly, encrypt this traditionally plain-text data to prevent prying eyes.
Partial is a drop-in replcement for the CoreDNS file plugin to provide semi-authoritative DNS zones.
A semi-authoritative zone enables you to provide authoritative records for a given zone for records the DNS server is aware of, and forwarding all unknown requests to an upstream server.
Available as a CoreDNS plugin, Partial is a drop-in replacement for the CoreDNS file plugin that allows for partially or semi-authoritative DNS zones, and is available on Github at https://github.com/charlesportwoodii/coredns-partial.
Automate backups on systemd-enabled Linux distributions to a encrypted BTRFS store with Restic and Minio.
If you’ve ever lost an important document or file you know how essential timely and reliable backups are. Getting backups done effeciently can prove to be challenge however, especially on Linux where a dozen different tools exist and do a variation on the same theme.
Until recently I’ve been using Duplicati which is an excellent tool, but struggles to start reliably on newer Linux kernel version, resulting in inconsistent backup states and data loss when you need to recover something.
In this article I’ll cover how I automate backups of all my Linux desktops, servers, and laptops to a locally encrypted BTRFS store, and off-site to a cloud provider.
Information for getting PCI passthrough working between Ubuntu 18.04 and Windows 10 using OVMF, VFIO, and Libvirt
Unable to tolerate the significant performance losses I was seeing on my aging i5-2500 desktop, I recently elected to upgrade my desktop to something a bit more powerful that would enable me to work faster and get more done.
While planning out this process, I stumbled up this article from mid 2017 detailing the process of getting GPU passthrough working on Fedora 26 with Ryzen.
Exhausted by the constant performance losses incurred by Spectre and Meltdown I was experiencing on my old i5-2500, and wanting to capitalize on the cost-per-core benefit Ryzen 2 offered, I decided to take the plunge into GPU passthrough and to see if it would be a viable long term solution for me, and my have I been pleased.
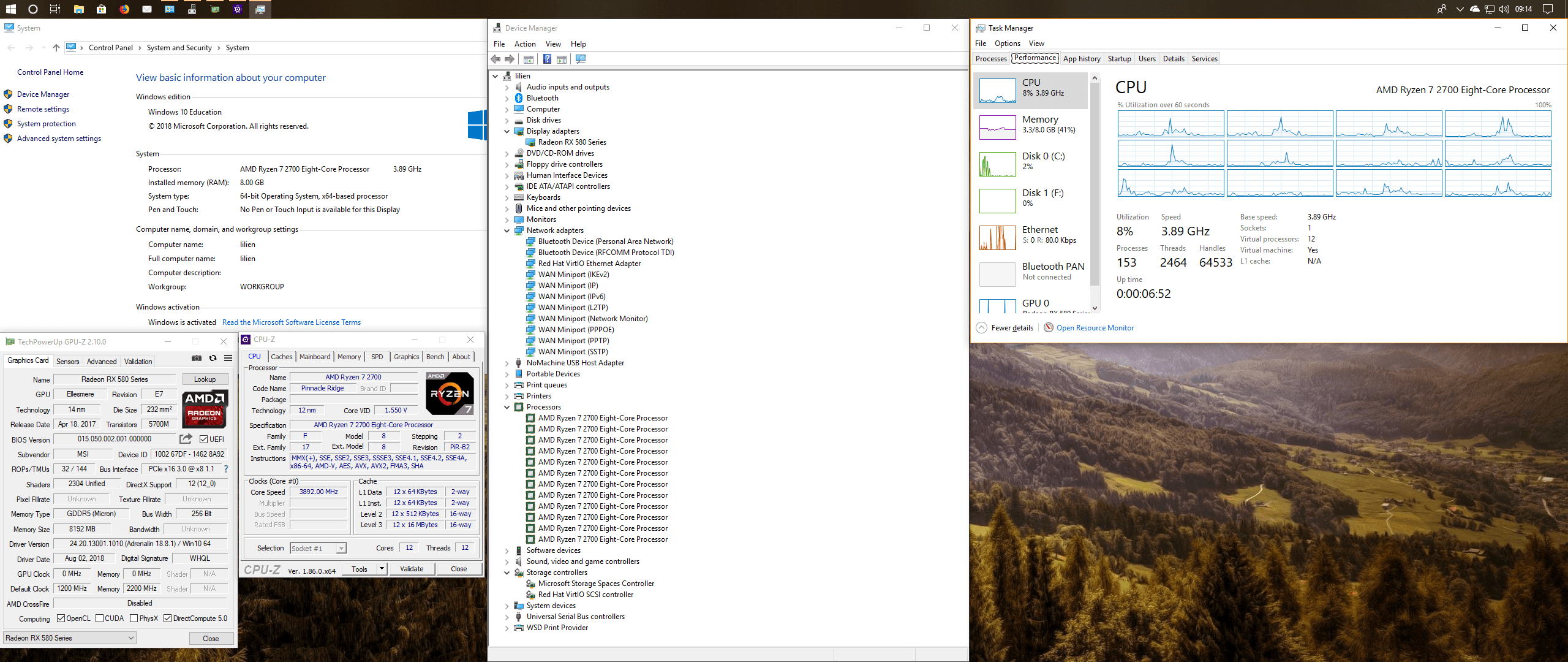
This write up details my experiences getting PCI passthrough working through Ubuntu 18.04 to Windows 10 using OVMF+VFIO and libvirt. While this document shouldn’t be considered a comprehensive guide, it will cover what I needed to do to get this working (mainly so I can set it back up again if I ever need to), while also covering a few tips and tricks I’ve learned along the way.
Installing Wireguard on Ubiquiti routers for faster home VPN
Wireguard is an extremely simple, fast, and modern VPN. With it’s introduction into the mainline linux kernel, Wireguard promises to provide a simpler, faster, and more secure way for setting up a VPN without needing to deal with traditional solutions like OpenVPN and L2TP/IPSEC, which can be cumbersome and slow.
In this article I’ll cover how to install Wireguard on a Ubiquiti router, and how to connect a remote client to it.